Emerging Threats and Solutions in Cybersecurity
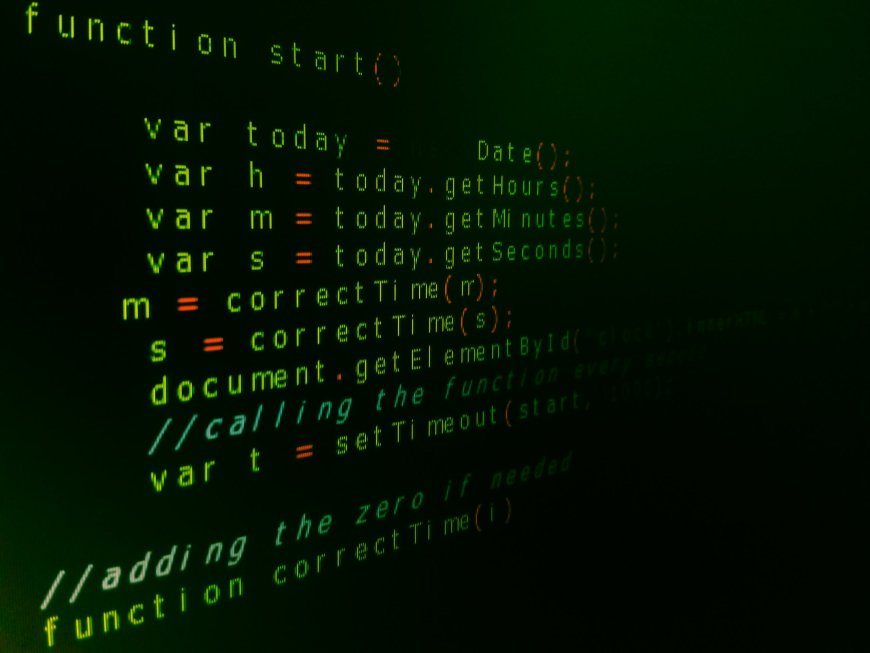
Navigating 2025, the terrain of cybersecurity has become more dangerous and complicated. The fast development of technology has created both great threats and hitherto unheard-of possibilities. While companies and people are rushing to apply creative defense systems, cybercriminals are using modern tools including artificial intelligence (AI) and quantum computing to exploit weaknesses. The developing cybersecurity risks of 2025 and the solutions required to guard personal and commercial data in this always-shifting digital world are investigated in this paper.
Rising Cybersecurity Concerns for 2025
1. Cyberattacks Driven by AI
In cybersecurity, artificial intelligence now serves as a two-edged blade. Cybercriminals are more complex and difficult to find even if they help identify dangers since they are utilizing it to automate attacks. Now common are phishing campaigns driven by artificial intelligence, deepfake frauds, and adaptive malware. By nearly perfect precision, these assaults can replicate human behavior, therefore avoiding conventional security protocols. For instance, phishing emails driven by artificial intelligence can plausibly pass for trusted people, thereby raising their success rate. Likewise, deepfake technology is being applied for fraudulent purposes including fabricating endorsements or tampering with systems of identity verification.
2. Evolution of Ransomware
Attacks involving ransomware have grown more frequent and sophisticated. Cybercriminals will be using "double extortion" strategies in 2025—encrypting data while threatening to release private information unless a ransom is paid. Ransomware-as---a- Service (RaaS) has also democratized cybercrime, allowing even low-skilled players to carry out advanced assaults. The main targets still are financial institutions, healthcare systems, and critical infrastructure. These strikes can have knock-on repercussions throughout whole sectors.
3. Challenges of Quantum Computing
Conventional encryption systems are seriously threatened by quantum computers. Although "harvest now, decrypt later" techniques are already being used by enemies to gather encrypted data for future decryption as quantum capabilities evolve, real quantum attacks still seem years away.
4. Weaknesses in Supply Chains
Attacks on supply chains keep being a major issue. Targeting third-party providers, cyber criminals use the linked character of modern supply chains to enter bigger companies. These leaks can sweep throughout systems and cause general disturbance.
5. Advanced Social Engineering
AI tools have helped social engineering techniques grow increasingly complex. Realistic audio or video impersonations created using deep-fake technology are misleading even the most alert people. Phishing campaigns or financial fraud operations frequently use these methods.
Techniques for Guarding Corporate and Personal Information
Businesses and people must implement proactive, multi-layered cybersecurity plans to tackle these new risks.
1.Accept the Zero Trust Security Model.
Operating on the idea of "never trust, always verify," the Zero Trust model assumes that every contact calls for constant authentication and tight access limits since no user or tool is naturally trustworthy35. This method works very well for reducing ransomware threats and safeguarding remote work setups.
· Zero Trust's main components are:
· MFA, or multiple-factor authentication
· Network micro-segregation
· Continuous observation of user behavior
2. Implement Innovative Encryption Methods
Data security still revolves mostly around encryption. Companies should make investments in cutting-edge encryption techniques resistant to present as well as future threats, including quantum computing. End-to- end encryption guarantees that private information is safe both in transit and in storage.
3. Proceed to quantum-resistant cryptography.
Companies should start using quantum-resistant cryptography methods to get ready for the quantum age. This shift will protect private information from any future decoding by quantum computers56.
4. Enhance Supply Chain Security
To lower supply chain risks, companies must do extensive security checks of their partners and vendors. Strict access policies and ongoing third-party activity monitoring help to find weaknesses early on.
5. Purchase AI-Powered Security Instruments
Leveraged as a defensive tool, artificial intelligence may foresee attacks, automate incident responses, and instantly identify anomalies.
· Predictive analytics find possible weaknesses before they are taken advantage of.
· Automated reactions have faster neutralizing power than human interventions.
6. Constant Staff Development
One of the weakest ties in cybersecurity still is human mistakes. Frequent training courses can enable staff members to follow the best standards for data security, avoid social engineering traps, and identify phishing efforts. Additionally helping staff members be ready for real-world events are simulated by phishing drills.
7. Apply strong backup plans.
Recovering against ransomware attacks or other data breaches calls for a thorough backup strategy. Companies should make sure backups are routinely verified for dependability and keep several copies of important data across secure sites.
8. Improve Cloud Safety
Securing cloud settings is becoming vital given the growing reliance on cloud services. Tools for cloud security posture management (CSPM) can help find misconfigurations and enforce security policy compliance.
Cyberspace Future Patterns
Looking forward, numerous trends will define the scene of cybersecurity:
· Governments all around are passing tougher data privacy rules, which force companies to implement more solid compliance policies.
· Cyber Insurance: Insurance companies are tightening policies on policyholders as cyber threats rise, therefore encouraging improved security methods.
· Public-private cooperation will be very important in addressing worldwide cyber threats utilizing information exchange and coordinated actions.
In 2025 cybersecurity calls for awareness, creativity, and flexibility. Comprehensive defense tactics are more important now than artificial intelligence-powered attacks, ransomware evolution, quantum computing threats, and supply chain vulnerabilities are rising in prominence. Businesses and people may keep ahead of new dangers by implementing cutting-edge technologies such as quantum-resistant cryptography and AI-driven security solutions and by encouraging a cybersecurity consciousness.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0



































